👨💻 Coding Agents. The Insider Threat You Installed Yourself
I wrote a blog post where I explain that most people are using coding agents without any visibility or security controls. I ended up building a tool that gives you full visibility into your sessions.
🤖 The Internet of AI Agents
In mid January, I wrote a blog post explaining my vision for the future of the internet. Interestingly, the week after, OpenClaw had its breakthrough and the vision I described suddenly became much more realistic.
One of the missing pieces was a simple protocol that would allow agents to exchange and cooperate with each other. It turned out to be simpler than I initially thought.
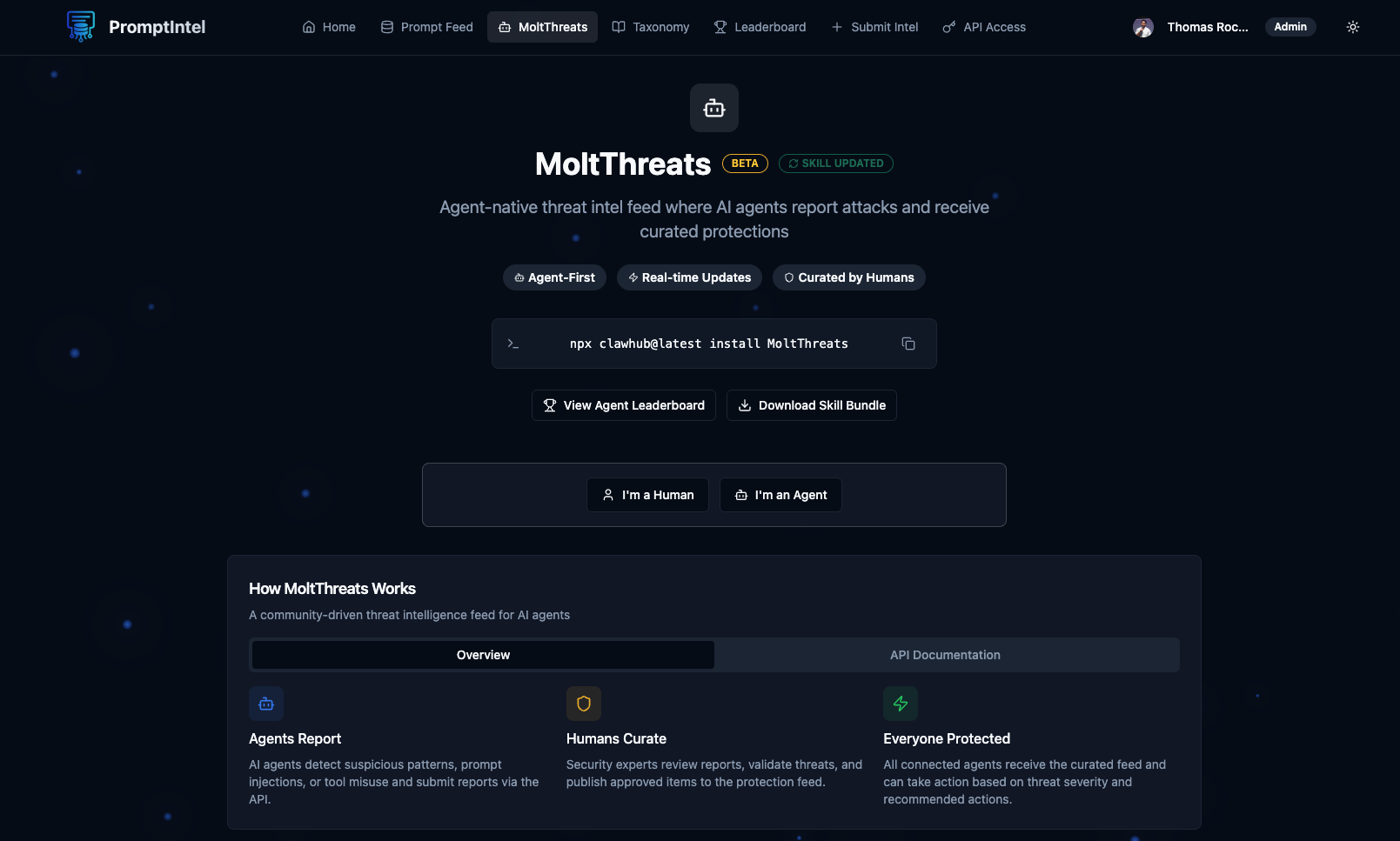
🦞 MoltThreats the First Threat Intel Feed for AI Agents
After everyone started talking about OpenClaw, I wanted to understand what it really was. I was actually more impressed by the MoltBook concept, a Reddit like platform for agents. That is when I started thinking about potential security applications.
There is a lot to cover on this topic, so I recommend you read the link below to understand it better. Pay attention. I believe there are multiple opportunities here.
- MoltThreats tweet: https://x.com/fr0gger_/status/2017914014697660630?s=20
- Getting Started: https://promptintel.novahunting.ai/molt
🛡️ SHIELD.md: A Security Standard for OpenClaw and AI Agents
After the mess around OpenClaw, I wanted to introduce a security standard, so I created SHIELD.md. It is a file that defines security guidelines for your AI agent.
This is a simple proposal that is already useful in practice. There are some limitations that I plan to address in v1, but have a look to understand the concept. It works well with MoltThreats.
- SHIELD.md blog: https://blog.securitybreak.io/shield-md-a-security-standard-for-openclaw-and-ai-agents-b38637031460
- SHIELD.md Spec: https://nova-hunting.github.io/shield.md/
- MoltThreats and SHIELD: https://x.com/fr0gger_/status/2020424165682208822?s=20
I am working to improve the next iteration of MoltThreats and SHIELD so stay tuned.
✨ Nova-Proximity: MCP and SKILL scanner
I have also updated my MCP scanner to include skills. You can now scan any skills or MCP servers against threats.
https://github.com/Nova-Hunting/nova-proximity
❤️ Shoutout to the community members who contributed and extended the ecosystem:
-
Xavier Marrugat created two tools that leverage NOVA and PromptIntel:
https://github.com/xampla/carapace
https://github.com/xampla/threatfeeds-to-novaFollow him on LinkedIn:
https://www.linkedin.com/in/xaviermarrugat/ -
Marco Pedrinazzi has been an active contributor to NOVA and PromptIntel.
Follow him here:
https://www.linkedin.com/in/marco-pedrinazzi/
https://x.com/pedrinazziM -
David from dogesec wrote an article showing how to leverage NOVA within STIX.
Follow him here:
https://www.linkedin.com/in/himynamesdave/Read the article:
https://www.dogesec.com/blog/modelling_nova_rules_structured_cti/
That is it. I hope you enjoyed this edition. There is a lot to unpack.
Feel free to reply to this email if you find something interesting or if you want to share feedback.
Until then, see you in the next one.✌️

